Protected: Bandit walkthrough
This presentation was hold on 20th May 2022 at The Bridge.
Workshop will be on July (day to be determined). Capacity: 3-5 people.
1- 7 November 2021
What I’ve learned
Ettercap-graphical and arp poisoning attack | net-tools utilities | openVAS | Traffic monitorization with Wireshark.
Reading list
- ¿El proceso «pingsender.exe» intenta conectarse a Internet? Esto es lo que debes saber.
- Nmap syntax: https://nmap.org/book/man-port-scanning-techniques.html
- Cómo listar y administrar servicios en Linux: https://www.hostinger.es/tutoriales/administrar-y-listar-servicios-en-linux
- SYN cookies: https://es.wikipedia.org/wiki/SYN_cookies
- Iptables’s week:
– A Deep Dive into Iptables and Netfilter Architecture: https://www.digitalocean.com/community/tutorials/a-deep-dive-into-iptables-and-netfilter-architecture
– Qué es iptables: https://openwebinars.net/blog/que-es-iptables/
I’ve enjoyed
Getting to know the principles of a firewall.
18 – 31 October 2021
What I’ve learned
Introduction to security. Red Team. OSINT (Open Source Intelligence) report elaboration using: shodan.io (with dorks), search.censys.io, nmap, spiderfoot, recon-ng, sublist3r, karma, theHarvester, maltego, nessus essentials, nikto, sherlock, profil3r, osintgram, FOCA, Google dorks, wigle.net, ItIsMeCall911/Awesome-Telegram-OSINT, and a buch of cool and open source tools (including those to mask identity). Free VPN like windscribe or ProtonVPN.
Reading list
- Chapter 3: Redes de computadoras. Un enfoque descendente. James F. Kurose. | La capa de transporte Download.
- What are black box, grey box, and white box penetration testing? [Updated 2020
I’ve enjoyed:
- Making a map for the OSINT presentation. For that I’ve discovered the land of the fantasy map generators. For our end, we’ve used: Azgaard’s Fantasy Map Generator.
11 – 17 October 2021
What I’ve learned:
We’ve started with the RedTeam block. First module is introductory and it’s oriented to resume main methodologies of attack | APT (Advanced Persistent Threat), 0Day exploit – 0Day Attack | Pentest phases | Mitre ATT&CK (“Adversarial Tactics, Techniques, and Common Knowledge.”) Framework | Risks analysis.
Reading list:
- Chapter 3: Redes de computadoras. Un enfoque descendente. James F. Kurose. | La capa de transporte Download.
- Common Vulnerability Scoring System.
- How CT fits into the wider Web PKI ecosystem.
- Network Commands.
- What are Certificate Authorities & Trust Hierarchies?
4 – 10 October 2021
What I’ve learned:
Basic on TCP/IP protocol. The OSI model. More deeply, we’ve seen some protocols from the Application layer (SMTP, POP, IMAP, SSH, RCP, DNS, FTP). We’ve started with crytography, hashes and public and private keys. Challenge this week was about stablishing a TCP connection with another VM.
Reading list:
- Chapter 1-2: Redes de computadoras. Un enfoque descendente. James F. Kurose. Download.
Group project:
- We’ve worked on the SMTP protocol in the Application layer (with Alejandro Mora). To explain it, we’ve implemented a basic mail server using Postfix on Kali. After that, we’ve captured traffic (using wireshark) to explain SMTP commands (HELO/EHLO, 220 OK, 250-STARTTLS , RCPT, RSET, QUIT…) and some extensions. Our presentation.
What I’ve enjoyed:
The amount of tweets from people pretending to be an expert about BGP and DNS. It was fun for that to be on the news.
Some serious reading about BGP and facebook
27 September – 3 October 2021
What I’ve learned:
Python scripting logic, no classes or objets yet, just the workaround of basic problems with functions, conditionals and loop iterations.
Reading list:
- Chapter 1-4: Programación shell en Unix/Linux (sh(Bourne), ksh, bash), by Christine Deffaix Rémy, published by Ediciones ENI, series “Recursos Informáticos”, 978-2-7460-5474-4, April 2010. Download index.
Group project:
- We’ve worked on these exercises (basket and ticketing), providing a solution for one of them (ticketing) as a group (our code). I wanted to implement classes and go a little further with an advanced menu, so here is my code for that.
What I’ve enjoyed:
Mathematical focus on problem resolutions. We’ve made the clasic “Piedra, papel o tijeras” (https://github.com/amandaguglieri/thebridge/tree/main/game_piedra-papel-tijeras) applying a module operation.
Stuck in:
Leviathan: Level 1 -> Level 2
20-26 September 2021
What I’ve learned:
Bash scripting | Introduction to Python3.
Reading list:
- Chapter 14 of book: Linux Basics for Hackers Getting Started with Networking, Scripting, and Security in Kali
- Horizontal Privilege Escalation: What is it and how to find them?, by The Infosec Student.
- Introductory Networking from tryhackme.com.
-
The 101 of ELF files on Linux: Understanding and Analysis, by Michael Boelen.
What I’ve enjoyed:
Since, I’ve noticed some webs have 3306 port open, I felt curious about how to exploit that (in one of my sites, of course). I’ve read this article (https://www.hackingarticles.in/penetration-testing-on-mysql-port-3306/) and tried to replicate it unsuccessfully. It was worthy the try though.
Also, an interesting concept I didn’t know about was ID scanning in wordpres. It’s something remarkably easy. By adding ?author={1andsoon} like this
https://anotherwordpresssite.com/?author=1
you can get the list of users of a site.
What I learned:
What happen when turning on a computer? | What is a VM? | VM Networks Configuration. | Basic linux commands. | Basic grep. | Basic Bash.
Reading list:
- GREP cheat sheet.
- Bit SUID en shell script (I).
- Bit SUID en shell script (II).
- Chapter 12 and 13 of book: Linux Basics for Hackers Getting Started with Networking, Scripting, and Security in Kali
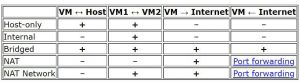
- What I’ve enjoyed: deep understanding of how netwotks work at virtual machines in VirtualBox. I love this table: